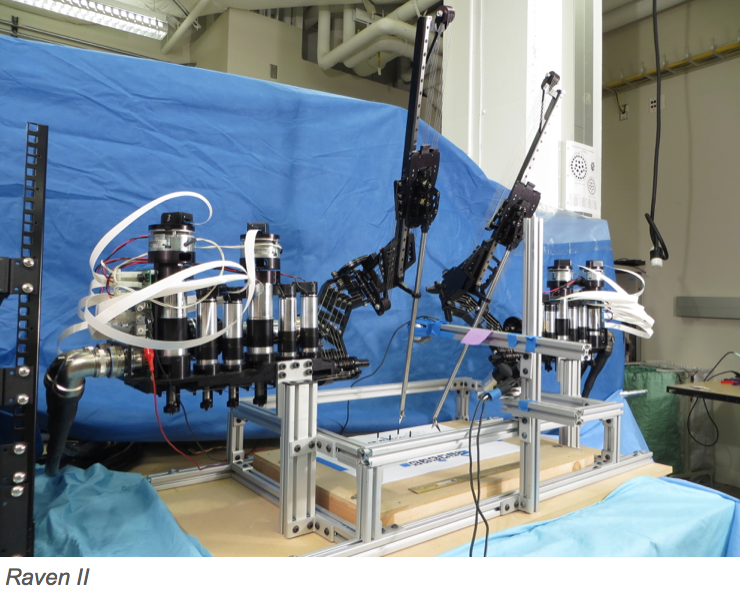
 It began as a surgical device for the military, one that could fit in an armored vehicle in the combat zone. However, the robot – named Raven II – became a strong platform for advancing the software, the control, and network security for medical robotics. Motherboard visited the BioRobotics Lab at the University of Washington, illustrating what happens when you hack a surgical robot.
It began as a surgical device for the military, one that could fit in an armored vehicle in the combat zone. However, the robot – named Raven II – became a strong platform for advancing the software, the control, and network security for medical robotics. Motherboard visited the BioRobotics Lab at the University of Washington, illustrating what happens when you hack a surgical robot.
In the video, the online magazine speaks with electrical engineering professors, Dr. Howard Chizeck and Dr. Blake Hannaford, and researcher, Dr. Tamara Bonaci at the University of Washington. The opportunities in using a remote robotic machine are numerous; the most beneficial is that you can send a robot into dire conditions.
“There are many places you do not want to send humans – underwater, a biohazard area, through high temperature, firefighting, toxic areas, radioactivity, mining and space,” said Professor Chizeck. “If you’re sending a robot, but you still want to have control, you have a communication link. However, there’s the potential that the link can be compromised, so you want to keep that safe and secure.”
Because the distance between the robot operator and device is often extensive, there is an increased chance of interception. In order to keep the robot safe and secure, researchers in the lab must think like attackers – they become the hackers.
“My job is to try and hack the robot,” Dr. Bonaci said. “From this, we can see what safety measures need to be done.”
One hack called the “man in the middle attack” tricks the robot into thinking that it is talking to the surgeon, when, in reality, it is speaking with an attacker. A hacker interrupts the signal and controls the motion of the device, leading to a potentially fatal situation.
According to Professor Chizeck, these types of attacks have already been demonstrated in the operations of other medical devices, like pacemakers and insulin packs. Allowing hackers to penetrate the precarious, delicate movements of a surgeon is not only deadly, but also hard to detect, a “subtle assassination” with a minimal crime trail.
Before releasing Raven II to human operations, researchers will investigate all ways to intercept the device, finding the vulnerabilities before giving the hackers a chance to look for them.

