
UW EE researcher Tamara Bonaci.
Ars Technica sat down with UW EE lecturer and researcher Tamara Bonaci (Ph.D. ’15) to discuss the next generation of hacking — the brain. As we evolve our technical efficiencies, brain hacking appears a presumed next step in the development of computer hacking capabilities. According to Bonaci, it is not only presumed, but plausible.
Bonaci discussed how a video game could be used to covertly harvest neural responses to subliminal images. Her game, Flappy Whale, measured subjects’ reactions to relatively innocuous things, such as fast food restaurant logos. However, according to Bonaci, this same setup could be utilized to extract a person’s sensitive information, from an individual’s religious beliefs to medical conditions.
“Electrical signals produced by our body might contain sensitive information about us that we might not be willing to share with the world,” Bonaci said in the Ars article. “On top of that, we may be giving that information away without even being aware of it.”
The Flappy Whale scenario is known as a brain-computer interface (BCI). In this process, seven electrodes are connected to a player’s head and electroencephalography (EEG) signals are measured in real time. Because the logos were displayed for milliseconds at a time, the subjects weren’t consciously aware of them. Bonaci’s team was able to glean clues about the player’s thoughts and feelings by measuring the brain signals at the precise time the images were displayed.
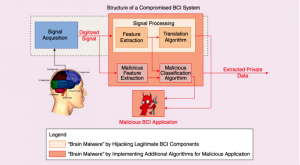
A simplified diagram of a compromised brain-computer interface system. Credit: Bonaci et al. via Ars Technica.
At this point, there’s no evidence that such brain hacking has ever been carried out in the real world. However, Bonaci said it wouldn’t be difficult for the makers of wearable software and hardware, such as virtual reality headgear, to covertly mine a host of physiological responses. The pilfered data could reveal insights about a person’s most intimate beliefs. Bonaci has also theorized that sensitive electric signals could be obtained by modifying BCI equipment used by doctors.
According to Bonaci, the extreme sensitivity of electrical signals produced by the brain should classify them as personally identifiable information (PII). Because of this, they would be subject to the same protections as names, addresses, ages and other types of PII. For the researchers and game developers who process responses for legitimate reasons, Bonaci suggests they develop measures to limit what’s collected instead of harvesting raw data. Sensitive data can teem into responses that might appear to contain only mundane or innocuous information.
“What else is hidden in an electrical signal that’s being used for a specific purpose?” Bonaci said in the article. “In most cases, when we measure, we don’t need the whole signal.”

